Space
靶机说明
QQ群:660930334
主机探测
1 | |
IP地址:192.168.2.38
nmap扫描
1、全端口扫描
1 | |
开放端口:22,80
2、详细信息扫描
1 | |
WEB渗透
1、访问80端口
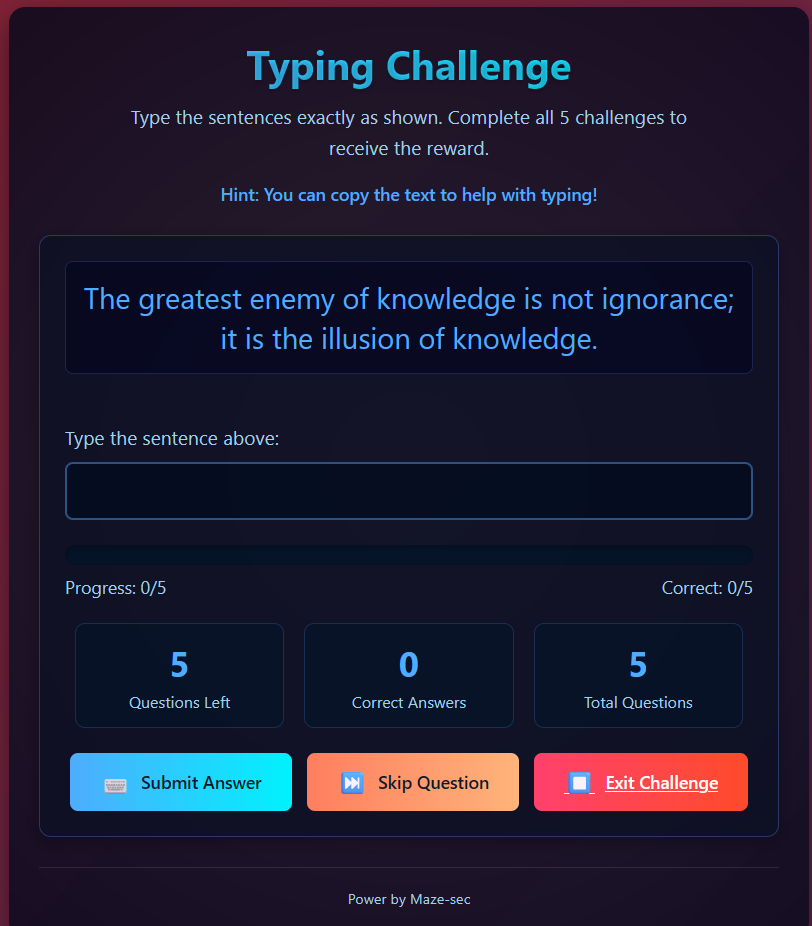
提示打字游戏,输入上面的文字,完成后有提示,根据步骤,完成上述的打字游戏,得到提示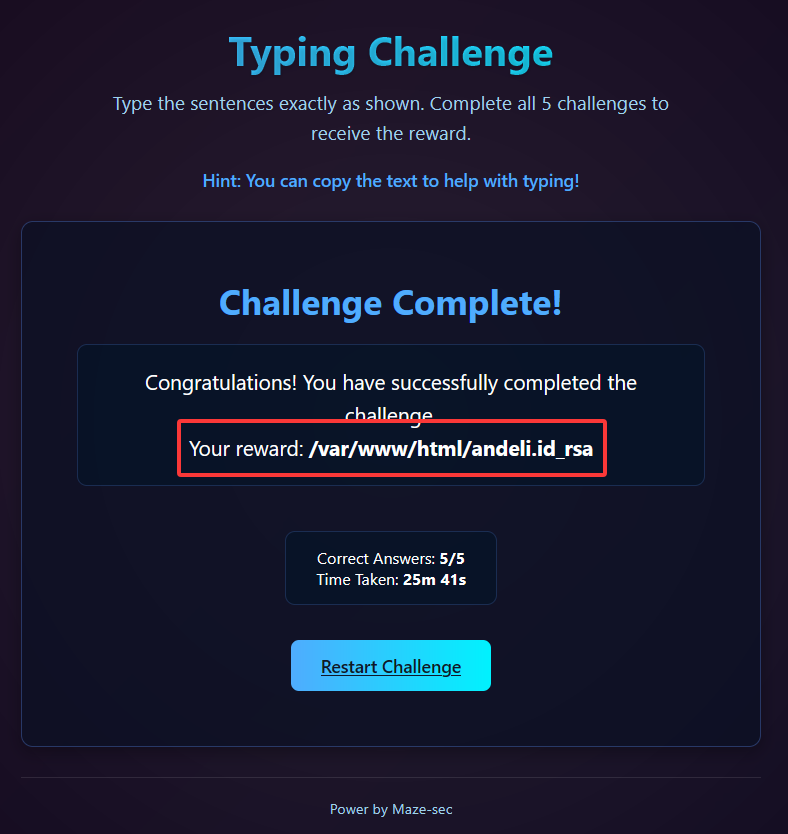
访问andeli.id_rsa,猜测是andeli用户的私钥
1 | |
2、目录爆破
1 | |
未发现其他目录
SSH渗透
1、ssh登录
尝试使用发现的私钥进行登录
保存私钥到本地
1
2
3
4
5
6
7
8
9
10
11┌──(root㉿kali)-[/tmp]
└─# wget http://192.168.2.38/andeli.id_rsa
--2025-06-23 23:01:22-- http://192.168.2.38/andeli.id_rsa
正在连接 192.168.2.38:80... 已连接。
已发出 HTTP 请求,正在等待回应... 200 OK
长度:2640 (2.6K)
正在保存至: “andeli.id_rsa”
andeli.id_rsa 100%[==================================================================>] 2.58K --.-KB/s 用时 0s
2025-06-23 23:01:22 (108 MB/s) - 已保存 “andeli.id_rsa” [2640/2640])修改私钥的权限 私钥的权限必须为600
1
2┌──(root㉿kali)-[/tmp]
└─# chmod 600 andeli.id_rsa尝试进行SSH登录
1
2
3
4
5
6
7
8
9
10
11ssh andeli@192.168.2.38 -i andeli.id_rsa
The authenticity of host '192.168.2.38 (192.168.2.38)' can't be established.
ED25519 key fingerprint is SHA256:O2iH79i8PgOwV/Kp8ekTYyGMG8iHT+YlWuYC85SbWSQ.
This host key is known by the following other names/addresses:
~/.ssh/known_hosts:5: [hashed name]
~/.ssh/known_hosts:7: [hashed name]
~/.ssh/known_hosts:8: [hashed name]
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.2.38' (ED25519) to the list of known hosts.
Load key "andeli.id_rsa": error in libcrypto
andeli@192.168.2.38's password:提示
Load key "andeli.id_rsa": error in libcrypto
2、CRLF remove
- 查看私钥里面不可见的字符每一行后面都有换行符,破坏了密钥结构
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40┌──(root㉿kali)-[/tmp]
└─# cat -A andeli.id_rsa
-----BEGIN OPENSSH PRIVATE KEY-----^M$
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABFwAAAAdzc2gtcn^M$
NhAAAAAwEAAQAAAYEA53wtJ27uQatcM+9fP8gZCT7ioVbSmFM5MWZZ+4ZZ/AJswfuI9ndz^M$
ADvJgrVgCj2//vHO7Hla0V4S7nHccrFLVuHxzxtcTXiITKmo+S0N0uBu0NdkzFwvmTPqR4^M$
tG/p1G6fgt9fms9tqw/A2EYf5Mk/cDv9OwhGldUArQZD9Dd/Zy7ZnRGhBVHm/HTxbwCad0^M$
n4Or9+PEUzJb5Uw+GG8A3P0J128BUlIxj4M2/I769q3xSG4EuT9kqAJXCdxAvIzZ6OIfEI^M$
9yFoRPbDLEe+95y5zoQpH6Yar5LqiK+X+YnxScWWwCe3r4BQJCiHT7LjIK0HH5YUMkFcr7^M$
t9QvNytztJPr2pVQET9UdkiN27u2DCygVw5y1q0rP3fCsEZDCUJxcfjn9PZw5IRzqJcO1B^M$
PIFacPpvv/jWI1DA1smd0+xr/AUWEBL4892GZ6hMR4uNLlva2iPoTs4cfZthecXWd0ImCy^M$
WcSe6S5pFNWZ+C/u7Td7l46xhlN6Tw/N2n1vQrupAAAFiGVFw9FlRcPRAAAAB3NzaC1yc2^M$
EAAAGBAOd8LSdu7kGrXDPvXz/IGQk+4qFW0phTOTFmWfuGWfwCbMH7iPZ3cwA7yYK1YAo9^M$
v/7xzux5WtFeEu5x3HKxS1bh8c8bXE14iEypqPktDdLgbtDXZMxcL5kz6keLRv6dRun4Lf^M$
X5rPbasPwNhGH+TJP3A7/TsIRpXVAK0GQ/Q3f2cu2Z0RoQVR5vx08W8AmndJ+Dq/fjxFMy^M$
W+VMPhhvANz9CddvAVJSMY+DNvyO+vat8UhuBLk/ZKgCVwncQLyM2ejiHxCPchaET2wyxH^M$
vvecuc6EKR+mGq+S6oivl/mJ8UnFlsAnt6+AUCQoh0+y4yCtBx+WFDJBXK+7fULzcrc7ST^M$
69qVUBE/VHZIjdu7tgwsoFcOctatKz93wrBGQwlCcXH45/T2cOSEc6iXDtQTyBWnD6b7/4^M$
1iNQwNbJndPsa/wFFhAS+PPdhmeoTEeLjS5b2toj6E7OHH2bYXnF1ndCJgslnEnukuaRTV^M$
mfgv7u03e5eOsYZTek8Pzdp9b0K7qQAAAAMBAAEAAAGADZsS3Fp8zodP6A2Nv6X3Mr/rei^M$
gsQJ/DoM+vQkVnTJSn587tAe+LZtwcv/4BIxj2C/oSe3u2hs/MtQ8kMemR0A1/tPiauEL5^M$
X+go8lxfj6F5YfUHC6vvcEXI42OgTJ7Z6C6aJPcD346DEI2K1meoAJpoMgIzQdUfkvDPxt^M$
ShFo/5uVVtIOcM2bkgMdnbSfX5uNZ4aR2OEIXJOPT+QVlk55hH183CeiAyoYjI1pdg0Nbw^M$
c51j0a+ULvvUOdQkSfDNUXD2G7I6UxIYCWOkh2uq0ddPU+Kwe7d12+cnvpub1BEtKAfCTG^M$
+NSL8y76bO2u/I7f/kPRzV7Hm4po0X5tZc0fn1tctqV2M+Hu+JoCrs/yVwo0CuA29h/pHh^M$
cg1cBzn7jISuDMIAU5l8/nzs4/q/AIfQzqywYUrt04dkcTBmoPyI1QZiD6LufA8L8ZYqQB^M$
TrzFsiw/DZNIUBW0XKECr3OQWiaTz44g1YWxKCpFjbXOcR+E25BNAL8eTl3D63OIIBAAAA^M$
wCszq5giZqnTab2lVPvtEDePkQHRBZzShp0xm5Ru5kCyzoCrkbyrHH0GhoH77RIItrwd/3^M$
XHXtzSAXsWWWiTIkO4zl9xV0dTs85mqeLCSQtS4yG8rz1vMsPCRPysKAo0pXMgvvKHqehl^M$
yIU99M3jVPbBiwIuXFGohWr4agxrqMOcsuNIPx3PFmO3lqo08blC+GUBerk8+fiIhkJWe0^M$
izzECGHV9xcCoOiwiAdQjr2hNzw9QfnpO/w9uWKmb1397aoQAAAMEA9D47nMj7KvxQtcWz^M$
XMXnbqE1Z9EDavrAoA1zZSLrGzJs7jWZyWJuKv450wuf2fqrMCMA0BVngNnS3ljXj04pAg^M$
EU5sFE8WOlVNvC9iSd1x5Nmo7DMItdKSHeJop63flzvi+7aNg9VX+qWS4oWMuMZ0m7Vupf^M$
mC+xiO+dng7BBFWKIYqrcdWCuBqA6TdOt/qycejhZpTzXzYs/KsmMBjl7uSuUQZu2f6GDl^M$
KvCxTjcpE8v7FgSPJv4TNg/DjbEneZAAAAwQDyoLp4Rapn6iXTKFqOAL/8m+uH8dqgB5OD^M$
560gxDEgINdYzxwfOz+p3gphSp54MczEJEnYnfvDfKYKR5ty0AXS0iEjEoGAQFXuRjWEQf^M$
MeTEb+VqnK/Y5sNXWwW/FVr2tTibwA0QlzQEtOOAceh5HcKrtKpxZjkK2d4odvY6MmbL/J^M$
Rtgh4TMV09EokfXACR9F/bNY5Lu+xFMef4NWtXl3e0GEZcoLDSsKCuloOJJoJR/IM1w8gs^M$
Bl1Hds+8Z7rpEAAAAMYW5kZWxpQFNwYWNlAQIDBAUGBw==^M$
-----END OPENSSH PRIVATE KEY-----^M$如果是使用复制粘贴,而非wget下载,就不会存在上述的问题
使用命令转换文件
1 | |
转换后还存在问题,直接复制粘贴秘钥
3、重新进行ssh登录
1 | |
USER FLAG
1 | |
提权
使用sudo -l进行查看,发现需要密码
1 | |
1、切换到另外一个用户
查看用户的home目录,发现存在一个user_data.json文件
查看发现是一些用户名和密码,同时观察到有一串密码是有颜色的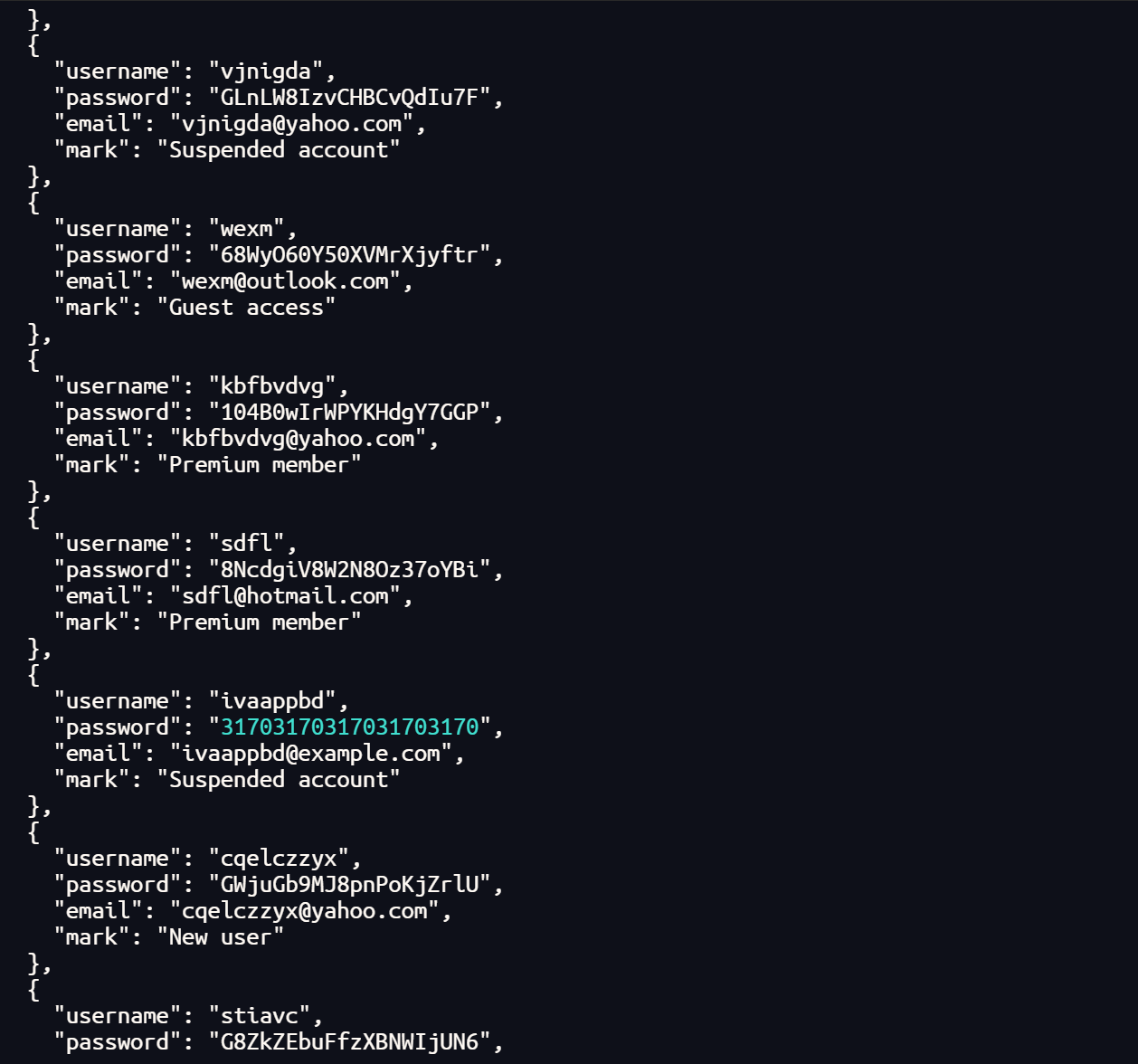
查看passwd文件,发现存在一个a3170用户
1 | |
尝试使用用户a3170和密码31703170317031703170进行登录
1 | |
2、dos2unix提权
使用sudo -l查看,发现dos2unix不需要密码也可执行root权限
1 | |
查看dos2unix的使用方法
1 | |
发现参数-n可以写入文件
尝试修改用户a3170的UID和GID和root一样,然后覆盖/etc/passwd文件
1 | |
1 | |
重新登录用户a3170
1 | |
ROOT FLAG
1 | |
Space
http://miao-sec.github.io/Maze-sec/Space/