1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
| ┌──(root㉿kali)-[/miaosec]
└─# nmap --min-rate 10000 -sT -sV -sC -O -p22,80,8080 192.168.2.47
Starting Nmap 7.94SVN ( https://nmap.org ) at 2026-01-15 16:53 CST
Nmap scan report for 192.168.2.47
Host is up (0.00084s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u1 (protocol 2.0)
| ssh-hostkey:
| 3072 f0:e6:24:fb:9e:b0:7a:1a:bd:f7:b1:85:23:7f:b1:6f (RSA)
| 256 99:c8:74:31:45:10:58:b0:ce:cc:63:b4:7a:82:57:3d (ECDSA)
|_ 256 60:da:3e:31:38:fa:b5:49:ab:48:c3:43:2c:9f:d1:32 (ED25519)
80/tcp open http Apache httpd 2.4.56 ((Debian))
|_http-title: Apache2 Debian Default Page: It works
|_http-server-header: Apache/2.4.56 (Debian)
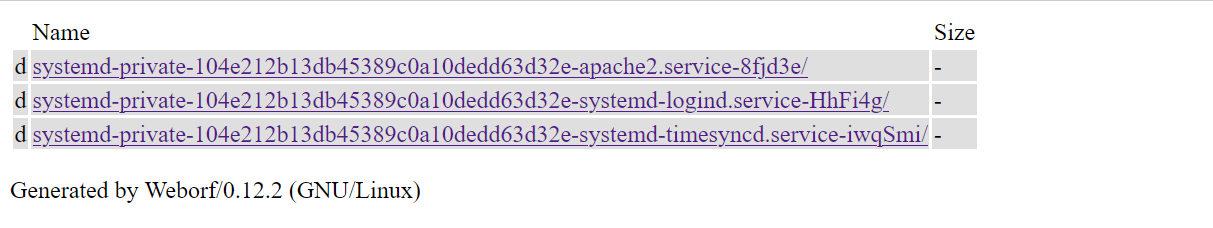
8080/tcp open http-proxy Weborf (GNU/Linux)
|_http-title: Weborf
| http-methods:
|_ Potentially risky methods: PUT DELETE PROPFIND MKCOL COPY MOVE
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.1 404 Page not found: Weborf (GNU/Linux)
| Content-Length: 202
| Content-Type: text/html
| <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"><html><head><title>Weborf</title></head><body> <H1>Error 404</H1>Page not found <p>Generated by Weborf/0.12.2 (GNU/Linux)</p></body></html>
| GetRequest:
| HTTP/1.1 200
| Server: Weborf (GNU/Linux)
| Content-Length: 960
| <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"><html><head><title>Weborf</title></head><body><table><tr><td></td><td>Name</td><td>Size</td></tr><tr style="background-color: #DFDFDF;"><td>d</td><td><a href="systemd-private-104e212b13db45389c0a10dedd63d32e-apache2.service-8fjd3e/">systemd-private-104e212b13db45389c0a10dedd63d32e-apache2.service-8fjd3e/</a></td><td>-</td></tr>
| style="background-color: #DFDFDF;"><td>d</td><td><a href="systemd-private-104e212b13db45389c0a10dedd63d32e-systemd-logind.service-HhFi4g/">systemd-private-104e212b13db45389c0a10dedd63d32e-systemd-logind.service-HhFi4g/</a></td><td>-</td></tr>
| style="background-color: #DFDFDF;"><td>d</td><td><a href="systemd-private-104e212b13db45389c0a10dedd63d32e-systemd-timesyncd.service-iwqSmi/">systemd-private-104e212b13db45389c0a10dedd63d32e-
| HTTPOptions, RTSPRequest:
| HTTP/1.1 200
| Server: Weborf (GNU/Linux)
| Allow: GET,POST,PUT,DELETE,OPTIONS,PROPFIND,MKCOL,COPY,MOVE
| DAV: 1,2
| DAV: <http://apache.org/dav/propset/fs/1>
| MS-Author-Via: DAV
| Socks5:
| HTTP/1.1 400 Bad request: Weborf (GNU/Linux)
| Content-Length: 199
| Content-Type: text/html
|_ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"><html><head><title>Weborf</title></head><body> <H1>Error 400</H1>Bad request <p>Generated by Weborf/0.12.2 (GNU/Linux)</p></body></html>
| http-webdav-scan:
| WebDAV type: Apache DAV
| Allowed Methods: GET,POST,PUT,DELETE,OPTIONS,PROPFIND,MKCOL,COPY,MOVE
|_ Server Type: Weborf (GNU/Linux)
|_http-server-header: Weborf (GNU/Linux)
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port8080-TCP:V=7.94SVN%I=7%D=1/15%Time=6968AB1A%P=x86_64-pc-linux-gnu%r
SF:(GetRequest,401,"HTTP/1\.1\x20200\r\nServer:\x20Weborf\x20\(GNU/Linux\)
SF:\r\nContent-Length:\x20960\r\n\r\n<!DOCTYPE\x20HTML\x20PUBLIC\x20\"-//W
SF:3C//DTD\x20HTML\x204\.01\x20Transitional//EN\"><html><head><title>Webor
SF:f</title></head><body><table><tr><td></td><td>Name</td><td>Size</td></t
SF:r><tr\x20style=\"background-color:\x20#DFDFDF;\"><td>d</td><td><a\x20hr
SF:ef=\"systemd-private-104e212b13db45389c0a10dedd63d32e-apache2\.service-
SF:8fjd3e/\">systemd-private-104e212b13db45389c0a10dedd63d32e-apache2\.ser
SF:vice-8fjd3e/</a></td><td>-</td></tr>\n<tr\x20style=\"background-color:\
SF:x20#DFDFDF;\"><td>d</td><td><a\x20href=\"systemd-private-104e212b13db45
SF:389c0a10dedd63d32e-systemd-logind\.service-HhFi4g/\">systemd-private-10
SF:4e212b13db45389c0a10dedd63d32e-systemd-logind\.service-HhFi4g/</a></td>
SF:<td>-</td></tr>\n<tr\x20style=\"background-color:\x20#DFDFDF;\"><td>d</
SF:td><td><a\x20href=\"systemd-private-104e212b13db45389c0a10dedd63d32e-sy
SF:stemd-timesyncd\.service-iwqSmi/\">systemd-private-104e212b13db45389c0a
SF:10dedd63d32e-")%r(HTTPOptions,B2,"HTTP/1\.1\x20200\r\nServer:\x20Weborf
SF:\x20\(GNU/Linux\)\r\nAllow:\x20GET,POST,PUT,DELETE,OPTIONS,PROPFIND,MKC
SF:OL,COPY,MOVE\r\nDAV:\x201,2\r\nDAV:\x20<http://apache\.org/dav/propset/
SF:fs/1>\r\nMS-Author-Via:\x20DAV\r\n\r\n")%r(RTSPRequest,B2,"HTTP/1\.1\x2
SF:0200\r\nServer:\x20Weborf\x20\(GNU/Linux\)\r\nAllow:\x20GET,POST,PUT,DE
SF:LETE,OPTIONS,PROPFIND,MKCOL,COPY,MOVE\r\nDAV:\x201,2\r\nDAV:\x20<http:/
SF:/apache\.org/dav/propset/fs/1>\r\nMS-Author-Via:\x20DAV\r\n\r\n")%r(Fou
SF:rOhFourRequest,12B,"HTTP/1\.1\x20404\x20Page\x20not\x20found:\x20Weborf
SF:\x20\(GNU/Linux\)\r\nContent-Length:\x20202\r\nContent-Type:\x20text/ht
SF:ml\r\n\r\n<!DOCTYPE\x20HTML\x20PUBLIC\x20\"-//W3C//DTD\x20HTML\x204\.01
SF:\x20Transitional//EN\"><html><head><title>Weborf</title></head><body>\x
SF:20<H1>Error\x20404</H1>Page\x20not\x20found\x20<p>Generated\x20by\x20We
SF:borf/0\.12\.2\x20\(GNU/Linux\)</p></body></html>")%r(Socks5,125,"HTTP/1
SF:\.1\x20400\x20Bad\x20request:\x20Weborf\x20\(GNU/Linux\)\r\nContent-Len
SF:gth:\x20199\r\nContent-Type:\x20text/html\r\n\r\n<!DOCTYPE\x20HTML\x20P
SF:UBLIC\x20\"-//W3C//DTD\x20HTML\x204\.01\x20Transitional//EN\"><html><he
SF:ad><title>Weborf</title></head><body>\x20<H1>Error\x20400</H1>Bad\x20re
SF:quest\x20<p>Generated\x20by\x20Weborf/0\.12\.2\x20\(GNU/Linux\)</p></bo
SF:dy></html>");
MAC Address: 08:00:27:4A:76:70 (Oracle VirtualBox virtual NIC)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Aggressive OS guesses: Linux 4.15 - 5.8 (99%), Linux 5.0 - 5.5 (99%), Linux 5.0 - 5.4 (97%), Linux 3.2 - 4.9 (96%), Linux 2.6.32 - 3.10 (96%), Linux 2.6.32 (96%), Linux 5.4 (95%), Linux 3.1 (95%), Linux 3.2 (95%), Linux 5.3 - 5.4 (95%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 147.24 seconds
|
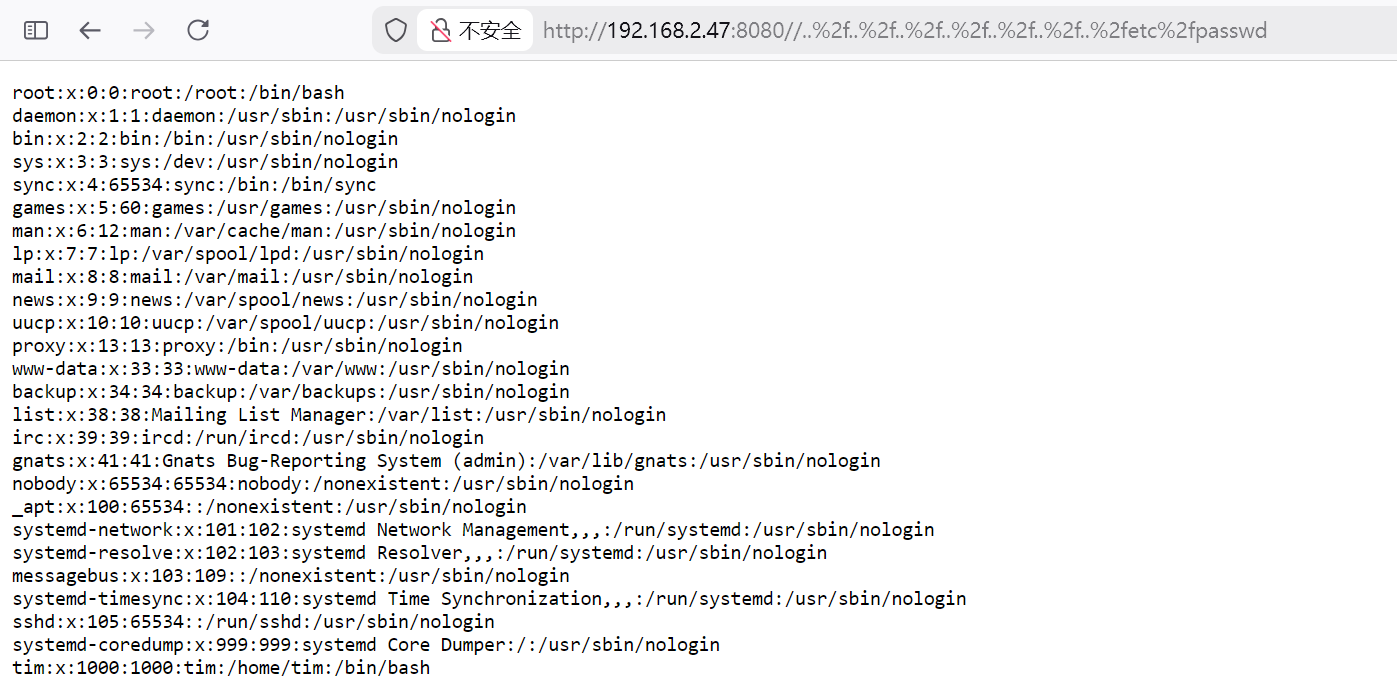 成功读取到用户`tim
成功读取到用户`tim