Mazesec_HackMe
靶机来源:QQ群-660930334
难度:Easy
思维导图: 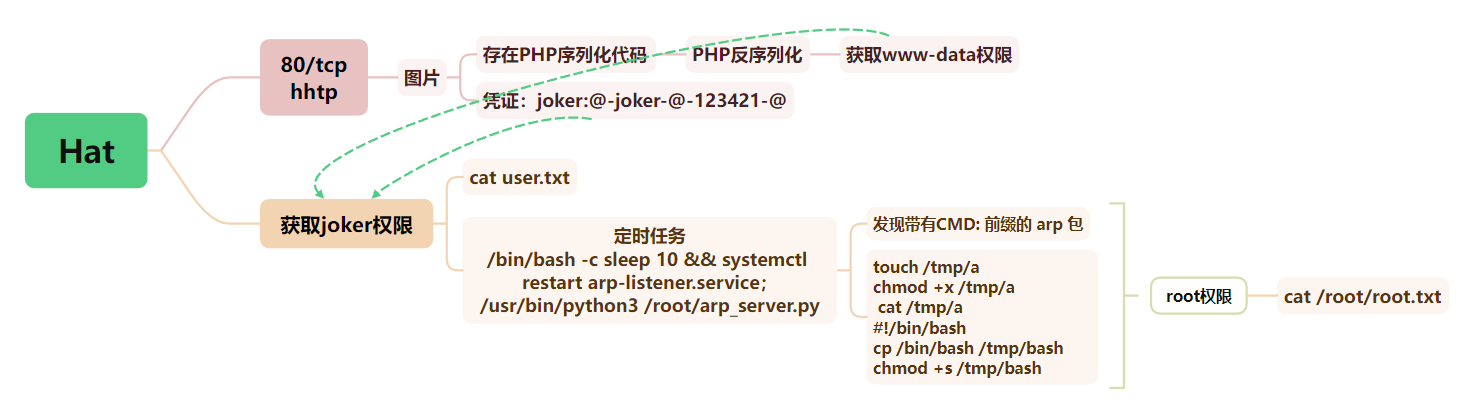
一、信息收集
1、主机探测
1 | |
靶机IP:192.168.2.11
2、端口扫描
1.全端口扫描
1 | |
开放端口:80
2.详细信息扫描
1 | |
3.udp扫描
1 | |
二、WEB渗透
1、80端口
访问80端口,是一张图片
2、目录扫描
1 | |
没有其他的信息
3、PHP反序列化
查看index.php,找到一段隐藏的源码
1 | |
是一个典型的 反序列化漏洞(Unserialize RCE),可能导致远程代码执行(RCE)
定义了三个类:
Starter:调用$this->obj(会触发__toString()如果是对象)Middle:其__toString()调用$this->target->run()Runner:其run()方法直接调用system($this->command)
Poc:
1 | |
使用post执行上面经过base64编码的序列化代码
1 | |
成功获取到shell
1 | |
稳定shell
1 | |
三、权限提升
1、获取joker权限
查看joker.jpg
1 | |
找到了凭证:joker:@-joker-@-123421-@, 我想着直接su joker,但是无法进行登录,卡了一会,尝试将22端口转发出来
1 | |
直接进行登录也行
1 | |
成功进行连接
1 | |
2、获取root权限
使用pspy64查看进程,发现root用户存在定时任务
1 | |
查看arp-listener.service服务信息
1 | |
【复现-111wp】
尝试单播 arp 请求,同时 tcpdump 监听过滤靶机的 arp 包,查看 arp 包信息
1 | |
尝试单播 arp 请求的同时使用tcpdump监听过滤靶机的 arp 包,查看 arp 包信息
1 | |
在 arp 包中发现了类似命令执行内容CMD: 00:51:33 up 7 min
使用脚本探测可能的利用方式
1 | |
测试发现,只有带有 CMD: 前缀的 arp 包会被执行,并通过 arp 包返回结果 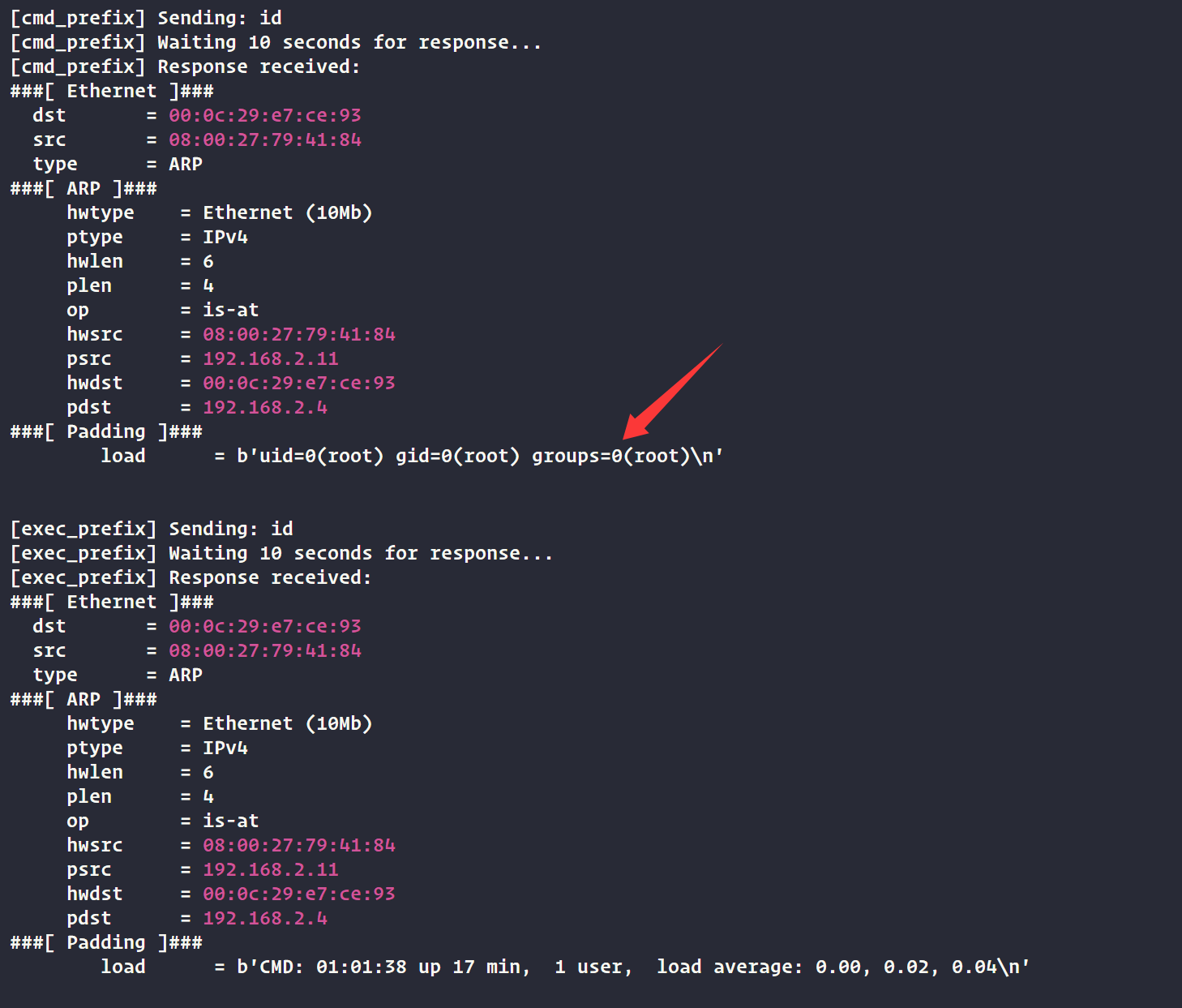
利用exp
1 | |
在靶机里面创建
1 | |
执行EXP
1 | |
成功获取到root权限
1 | |
四、查看FLAG
1 | |
Mazesec_HackMe
http://miao-sec.github.io/Maze-sec/Mazesec-HackMe/