Mazesec_Ezre
靶机来源:QQ群-660930334
难度:Baby
一、信息收集
1、主机探测
1 | |
靶机IP:192.168.2.95
2、端口扫描
1.全端口扫描
1 | |
开放端口:22、80
2.详细信息扫描
1 | |
3.udp扫描
1 | |
二、WEB渗透
1、80端口
访问80端口
1 | |
没有信息,进行目录扫描
2、目录扫描
1 | |
找到目录:dev
访问目录dev找到两个文件 
查看todo.txt 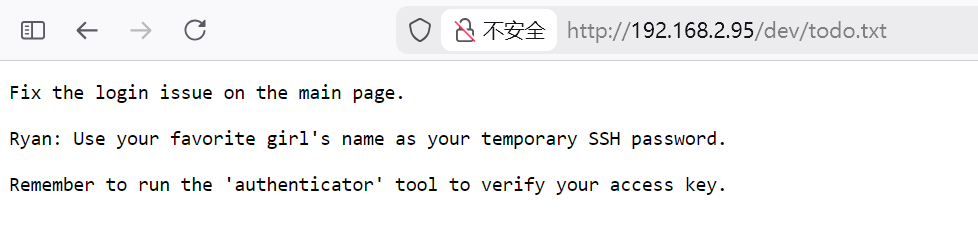 提示我们了SSH的账号是
提示我们了SSH的账号是Ryan,密码是你最喜欢的女孩的名字
同时还有一个二进制文件authenticator
三、RC4 流加密算法
反编译二进制文件authenticator 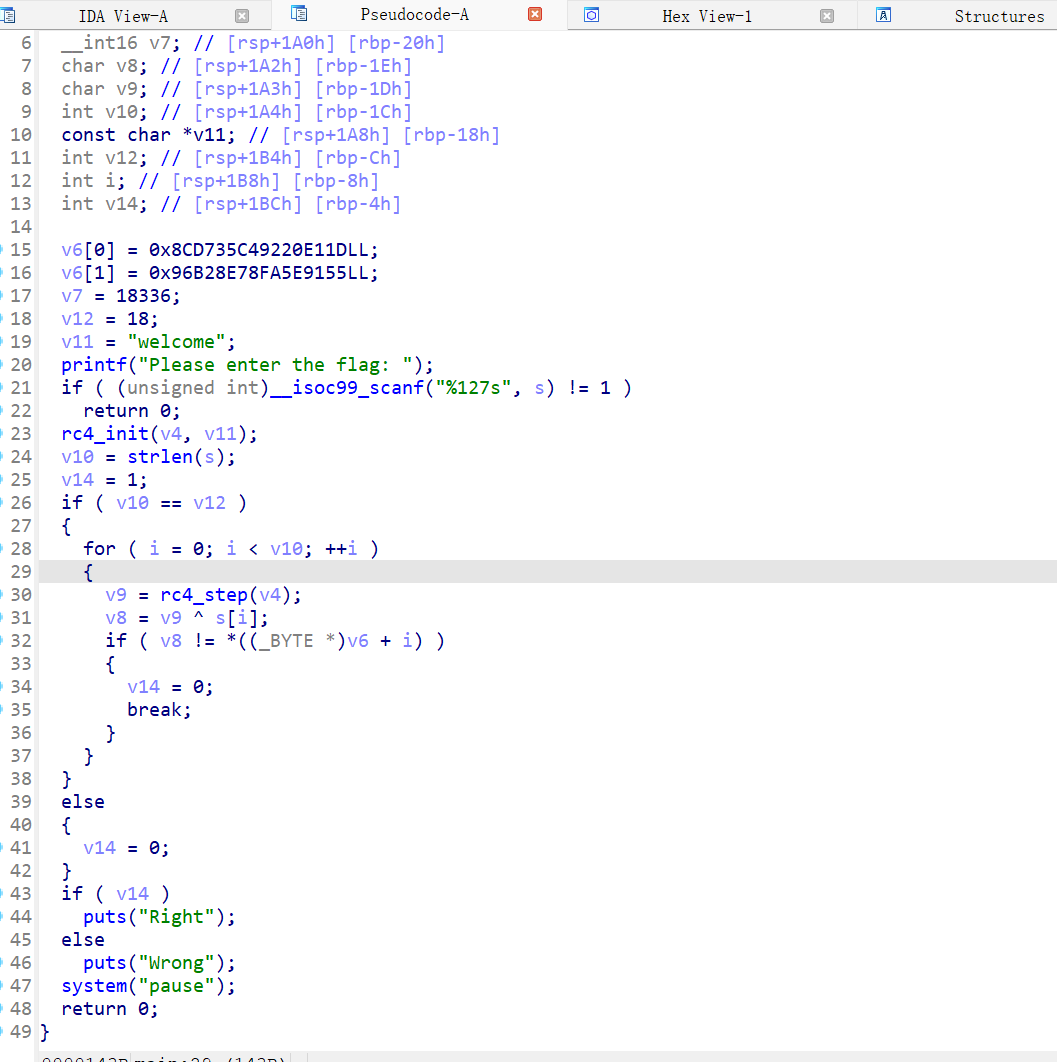
将反编译出来的源码丢给ai,得到Python脚本还原flag
1 | |
运行该脚本,得到FLAG
1 | |
成功获取到Ryan用户的ssh密码:sunninggirl
得到Ryan的权限
1 | |
四、权限提升
查看suid文件
1 | |
找到一个文件/usr/bin/super_checker具有suid权限
查看文件
1 | |
需要我们输入密码
使用strings进行查看
1 | |
- 程序会提示输入密码
- 如果正确 → 打印 “Access Granted!” 并执行
system("service --status-all") - 如果错误 → 打印 “Access Denied!”
因此可以输入正确的密码,然后劫持service进行提权
尝试对该文件进行反编译 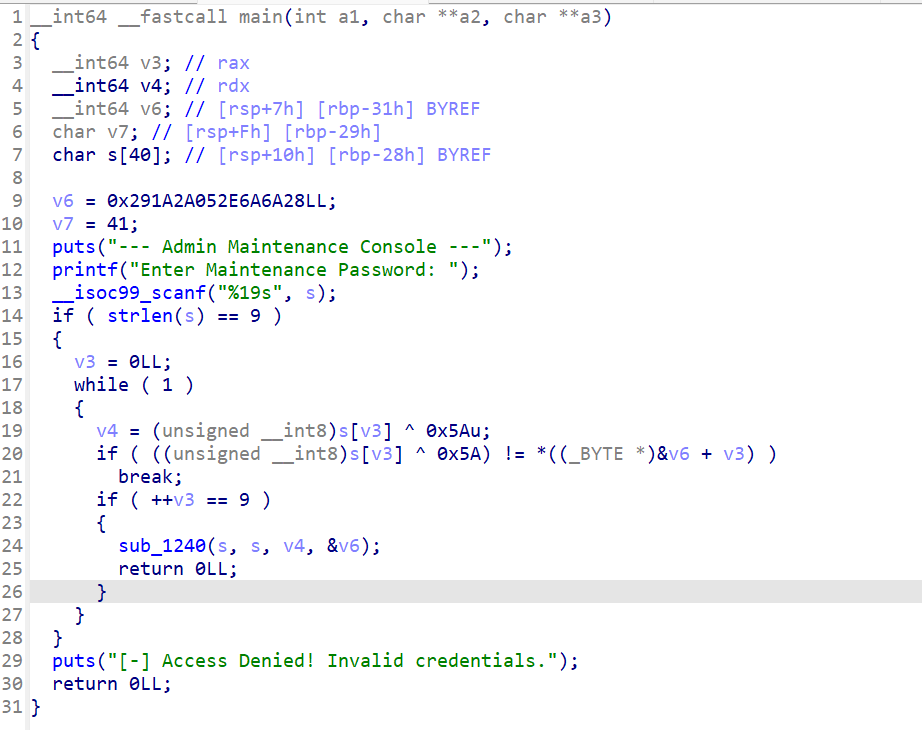
丢给ai,自动解出密码为:r00t_p@ss
那么就可以劫持service
- 创建恶意的
service
1 | |
- 将tmp目录加入到环境变量
1 | |
- 执行
/usr/bin/super_checker
1 | |
查看/tmp目录,成功写入了rootshell
1 | |
获取root权限
1 | |
五、查看FLAG
1 | |
Mazesec_Ezre
http://miao-sec.github.io/Maze-sec/Mazesec-Ezre/