13max
靶机说明
QQ群:660930334
一、主机探测
1 | |
IP地址:192.168.2.47
二、端口扫描
1、全端口扫描
1 | |
开放端口:21,22,80
2、详细信息扫描
1 | |
21端口:开放的服务是pyftplib
3、UDP端口扫描
1 | |
没有开放的端口
三、WEB渗透
访问80端口
需要我们输入加密的路径,去解锁掩藏的文件
- 访问
welcome,发现路径变为jrypbzr.gkg - 访问
config,发现路径变为pbasvt.gkg - 访问
readme,发现路径ernqzr.gkg
1、目录扫描
1 | |
进行目录扫描,发现welcome.txt对应jrypbzr.gkg,config.txt对应pbasvt.gkg,readme.txt对应ernqzr.gkg
经过测试发现,输入的路径需要经过rot13编码
2、ROT13读取文件
尝试将/etc/passwd编码后,进行输入,发现能够成功读取文件,同时发现两个用户welcome,max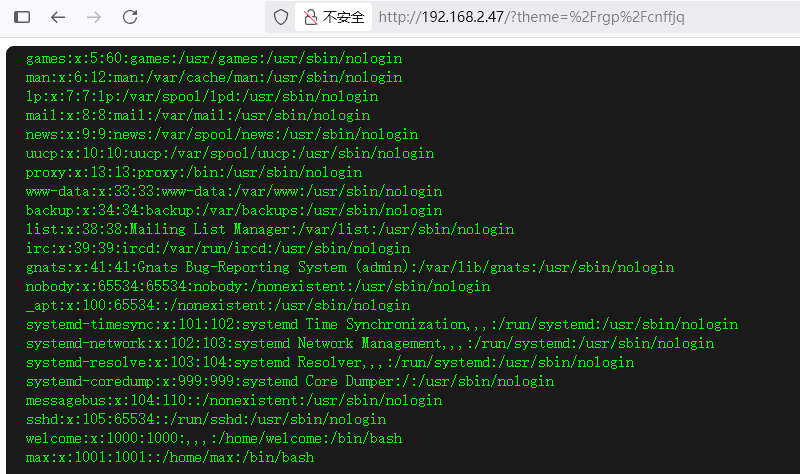
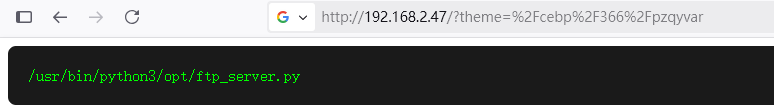
同时访问logs,发现存在文件ftp_server.log,是ftp的登录日志,同时发现开放着pid366
1 | |
尝试去读取PID里面的内容,/proc 目录存储了所有进程的运行时信息,每个pid对应一个子目录,发现存在目录/opt/ftp_server.py
读取/opt/ftp_server.py,找到了ftp的用户名和密码:ADMIN:12345
1 | |
四、FTP渗透
根据找到的用户名和密码,进行登录
1 | |
1、put-shell
上传一个反弹的shell,发现不解析,尝试上传phpinfo()
1 | |
1 | |
访问/opt/phpinfo.txt,找到被禁用的函数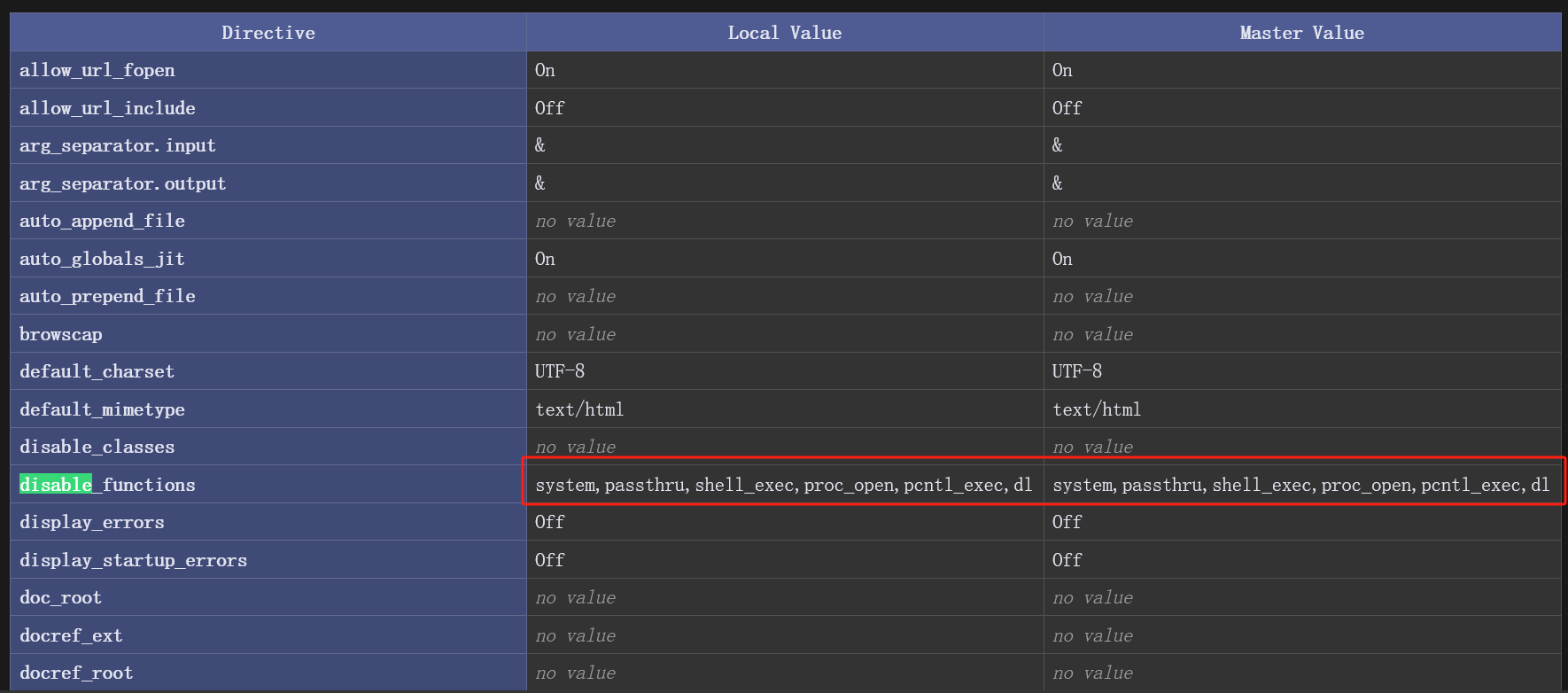
2、get-shell
使用下面的shell进行反弹
1 | |
访问/opt/rev.txt,成功获取到shell
1 | |
USER FLAG
在welcome用户下面,找到user.txt
1 | |
五、权限提升
1、获取welcome权限
1-cupp制作密码字典
在max用户目录下面,找到.hint,又找到.pucc,提示使用cupp.py
1 | |
使用welcome.txt里面的用户名,制作子典
1 | |
2、hydra爆破密码
1 | |
找到密码Zakaria2020
3、获得welcome权限
1 | |
2、获取root权限
使用linpeas.sh跑一遍,找到一个文件/usr/local/bin/supersuid
1 | |
或者查找和welcome相关的文件
1 | |
查看文件/usr/local/bin/supersuid,发现类似于网络进程监控netstat,ss
1 | |
查看文件的使用方法
1 | |
发现-F,可以读取文件,
1、读取文件
读取ssh的私钥或者/etc/shadow
读取
ssh私钥,发现没有文件1
2welcome@13max:/tmp$ /usr/local/bin/supersuid -F /root/.ssh/authorized_keys
Cannot find it.读取
/etc/shadow,找到root用户密码的哈希值1
2
3welcome@13max:/tmp$ /usr/local/bin/supersuid -F /etc/shadow
Error: an inet prefix is expected rather than "root:$6$Cax26XI4SpAAItdE$7iVSsRoQT/o0b3.V9jMiljdau506ePGmZLkIl5JH9COngDqdXJkGnizRIhaLJu/JbwWZ.7XyF/MwzuDusZJcg1:20273:0:99999:7::".
Cannot parse dst/src address.
2、john破解root-hash
1 | |
找到root用户的密码april7th
3、获得ROOT权限
1 | |
ROOT FLAG
1 | |
【总结】
1、PID读取文件
/proc 目录存储了所有进程的运行时信息,每个pid对应一个子目录,知道PID时,可以读取相关的信息,命令:/proc/pid/cmdline