1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
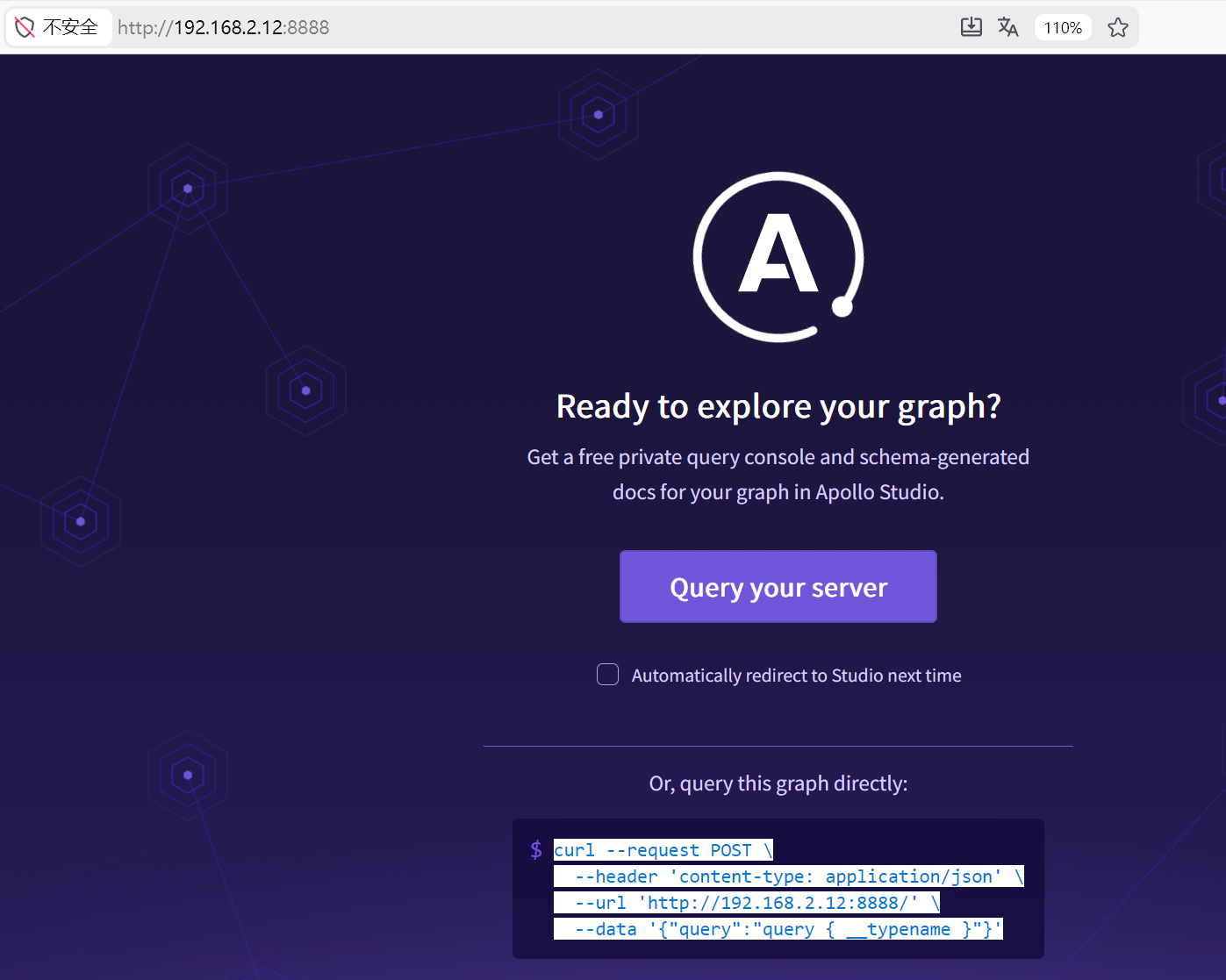
| ┌──(root㉿kali)-[~/miaosec]
└─# nmap --min-rate 10000 -sT -sC -sV -O -p22,8888 192.168.2.12
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-31 17:34 +0800
Nmap scan report for 192.168.2.12
Host is up (0.00073s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 10.0 (protocol 2.0)
8888/tcp open sun-answerbook?
| fingerprint-strings:
| DNSStatusRequestTCP, DNSVersionBindReqTCP, Help, JavaRMI, LSCP, RPCCheck, SSLSessionReq, TLSSessionReq, TerminalServerCookie:
| HTTP/1.1 400 Bad Request
| Connection: close
| FourOhFourRequest, GetRequest:
| HTTP/1.1 400 Bad Request
| Access-Control-Allow-Origin: *
| Content-Type: text/html; charset=utf-8
| Content-Length: 18
| ETag: W/"12-7JEJwpG8g89ii7CR/6hhfN27Q+k"
| Date: Tue, 31 Mar 2026 09:34:48 GMT
| Connection: close
| query missing.
| HTTPOptions:
| HTTP/1.1 204 No Content
| Access-Control-Allow-Origin: *
| Access-Control-Allow-Methods: GET,HEAD,PUT,PATCH,POST,DELETE
| Vary: Access-Control-Request-Headers
| Content-Length: 0
| Date: Tue, 31 Mar 2026 09:34:48 GMT
| Connection: close
| RTSPRequest:
| HTTP/1.1 204 No Content
| Access-Control-Allow-Origin: *
| Access-Control-Allow-Methods: GET,HEAD,PUT,PATCH,POST,DELETE
| Vary: Access-Control-Request-Headers
| Content-Length: 0
| Date: Tue, 31 Mar 2026 09:34:53 GMT
|_ Connection: close
...
MAC Address: 08:00:27:90:71:F5 (Oracle VirtualBox virtual NIC)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.19, OpenWrt 21.02 (Linux 5.4)
Network Distance: 1 hop
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 16.62 seconds
|